2-Factor Authentication¶
A 2-factor authentication mechanism (2FA) is being enforced for logins on HoreKa to improve security. In addition to the service password, a second value, the so-called second factor, has to be entered on every login.
2FA Basics¶
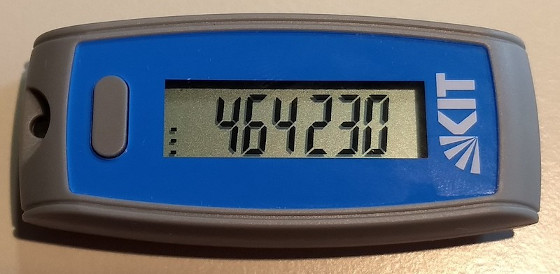
For HoreKa we use six-digit, auto-generated, time-dependent One-Time Passwords (TOTP). These passwords are generated by a piece of software which is part of a special hardware device (a Hardware Token), or by a software application running on a normal computing device (a Software Token).
The Token has to be synchronized with a central server before it can be used for authentication. After this it generates an endless stream of six-digit values that can be used as a second value besides the normal account password. Each of this values can only be used once, and the are only valid during a short interval of time. This makes it much harder for potential attackers to access the HPC systems, even if they should happen to know the regular service password.
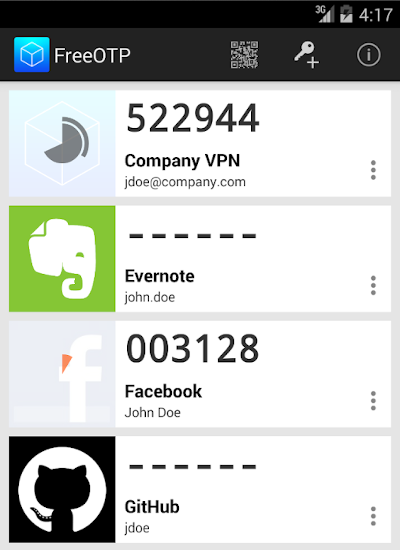
The most common solution is to use a mobile device (e.g. your smartphone or tablet) as a Software Token by installing one of the following recommended apps:
-
Authy for Mac, Windows or Linux
-
GNOME Authenticator for Linux
These are only suggestions. You can use any application compatible with the TOTP standard.
Software token handling
It is very important that the device that generates the One-Time Passwords and the device which is used to log into HoreKa are not the same. Otherwise an attacker who gains access to your system can steal both the service password and the secret key of the Software Token application, which allows them to generate One-Time Passwords and log into the HPC system without your knowledge.
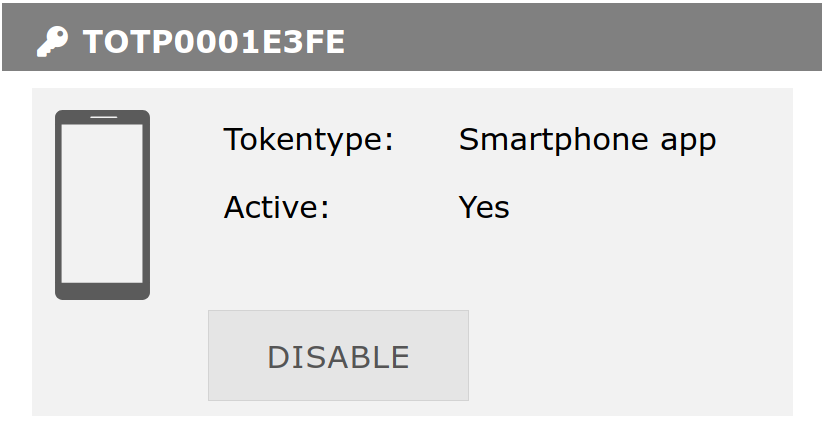
Token Management¶
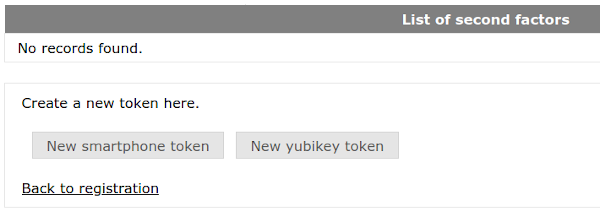
Tokens are managed via the My Tokens / Meine Token menu item under the Index / Übersicht menu entry on the central FeLS identity management platform. Here you can register, activate, deactivate and delete Tokens.
KIT users can also re-use their existing hardware and software tokens for the HPC systems, but have to manage them using the KIT self-service portal instead..
Registering a new Software or Hardware Token¶
Registering a new Token starts with a click on New smartphone token. If you happen to own a Yubikey USB Hardware Token made by the manufacturer [https://www.yubico.com Yubico], you can click on New Yubikey Token instead.
A new window opens. Click on Start to generate a new QR code. This may take a while.
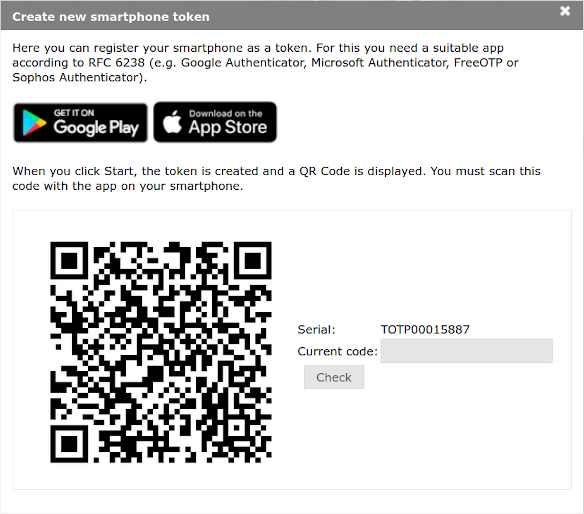
QR code handling
The QR code contains a key that has to remain secret. Only use the QR code to link your Software Token app with FeLS in the next step. Do not save the QR code, print it out or share it with someone else! You can always generate more codes later, if necessary.
Start the Software Token app on your separate device and scan the QR code. The exact process is a little bit different in every app, but it usually involves pressing on a Button with a Plus (+) sign or an icon of a QR code.
Once the QR code has been loaded into your Software Token app, it should now display a new entry called bwIDM. Generate an One-Time-Password by pressing on this entry or selecting the appropriate button/menu item. A six-digit code will be displayed. Enter this code into the field labeled Current code: in your browser window to prove that the app has been successfully linked, and then click on the Check button.
If everything worked as expected, you will be returned to the My Tokens screen and there will be a new entry for your Software Token. Make sure that it is marked as Active!
Repeat the process to register additional tokens. Please register at least a Backup TAN list in addition to the hardware/software token you plan to use regularly. If you only register a single token and happen to lose access to it, e.g. because you lose your device, uninstall the software token application or data gets deleted/corrupted, you will neither be able to log into the cluster system nor register a new token. The support teams are able to deactivate lost tokens, but this process will take its time.
Deactivating a Token¶
Click on the Disable button next to the Token entry on the My Tokens screen.
Deleting a Token¶
After a Token has been disabled, a new button labeled Delete will appear. Click on it to delete the Token.